Idea
I’ve been bouncing this around with a couple coworkers who have far more experience with networking than I do, for a month or so now. I bounced the idea off of them to make sure I was thinking about it correctly before I jumped in to a project that would possibly leave my entire LAN offline for hours, and it seems like this idea is sound.
My idea is to separate my home LAN into a management network and end-device network. My OPNSense router - a Protectli Vault v1211 - is a two-port firewall device. One WAN port and one LAN port. In order to separate my networks, I need a managed switch to run VLANs and set my ports.
As it stands, if anyone were to connect to my WAP (which is a neutered consumer-grade Netgear router running OpenWRT), they suddenly have access to my entire home network. Granted, I do have other stops in place in the form of SSH public key + password authentication, but my end goal is to have all management separated, with a jump server. Services should still be accessible to the end-device network, but gated with password authentication. Management portals such as firewall configuration, my TrueNAS web portal, etc, should be limited to the new subnet.
Diagram
Here’s an idea of what I want the end result to be:
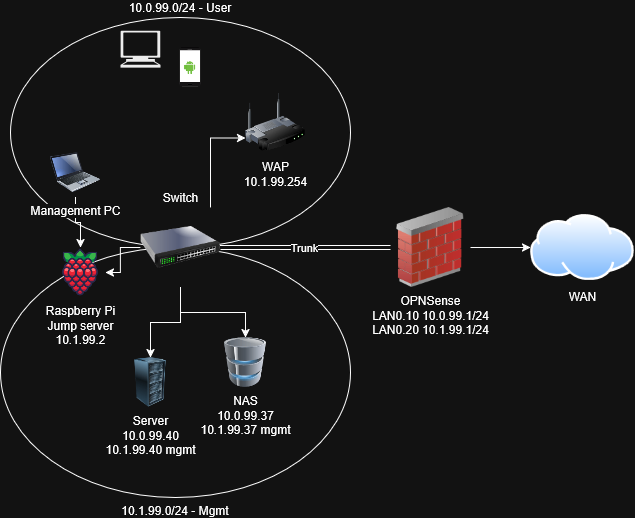
Note that eventually - not included in this diagram - I’d like to create a guest network, entirely isolated from the other LAN subnets, but if I get the RoaS configuration up and running I think that should be a breeze - create a third subnet on the router and switch, make the necessary switch port configurations, activate the 2.4gHz network on my WAP with a different default gateway, and create firewall rules to isolate traffic.
This also doesn’t include my Tailnet - I may be able to configure that to be my isolation, and may be overthinking this entirely, but I’d rather not rely fully on it. It’s great as a remote access solution, and I’ll probably reconfigure it to allow access to the management network in addition to the jump server. We’ll see how everything shakes out.
Next steps
I have configured RoaS before, but never in a “production” environment, and only on Cisco devices. I own, as already mentioned, an OPNSense router with the two ports, as well as a Netgear “business-grade” managed switch.
Now, the Netgear switch’s management capabilities are unfortunately gated behind a Netgear login, which I don’t have and I’m not going to create, and really pissed me off. For a device that I bought and paid for, and I could easily configure completely offline, I have to connect to the internet and log in to this stupid cloud account just to get access to the local management features. Fuck off, Netgear.
Anyway, like I said I have configured on Cisco devices before. Making the jump to two unknown devices was going to be a stretch, in addition to the frustrating Netgear account issues. Plus, since I can’t access the damn portal, I have no idea if the configuration options I need are there in the Netgear interface.
Fortunately for me, my workplace has a glut of older unused Cisco devices (routers and switches), and I got the go-ahead to grab a switch to do a proof-of-concept configuration. Now I just have to figure out how to configure on my router - and I did find a couple posts stating they were able to configure RoaS on OPNSense a while back that could be helpful in that regard.
I’m going to hop into Packet Tracer as well to do a refresher on all Cisco devices before actually running a test on the LAN. I’ll be documenting steps in separate more technical posts, but I wanted to pound out the idea on my keyboard before getting into the nitty gritty of it.
EOF